Garth supports two token types for GitLab authentication. Use a Group Access Token if you are on GitLab Premium or Ultimate — it creates a managed bot user and simplifies permission management across the organization. Otherwise, use a Personal Access Token from a dedicated service account.Documentation Index
Fetch the complete documentation index at: https://docs.heygarth.ai/llms.txt
Use this file to discover all available pages before exploring further.
Step 1: Create an access token
Option A — Group Access Token (recommended for Premium/Ultimate)
Option A — Group Access Token (recommended for Premium/Ultimate)
Option B — Personal Access Token (for non-Premium tiers)
Option B — Personal Access Token (for non-Premium tiers)
Step 2: Link to Garth
Open Garth integrations
Log into the Garth dashboard and navigate to Settings → Integrations.
Bind the token
Select the GitLab tab. Enter your GitLab URL (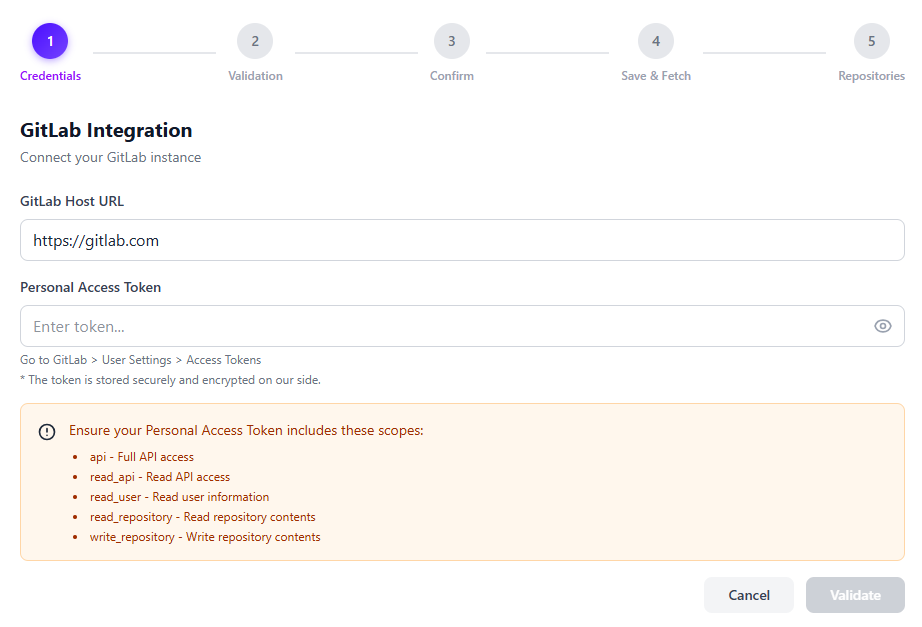
https://gitlab.com)
and the Access Token you just created, then click Validate.
Install repositories
After validation, select the repositories you want Garth to review and click Install Repositories.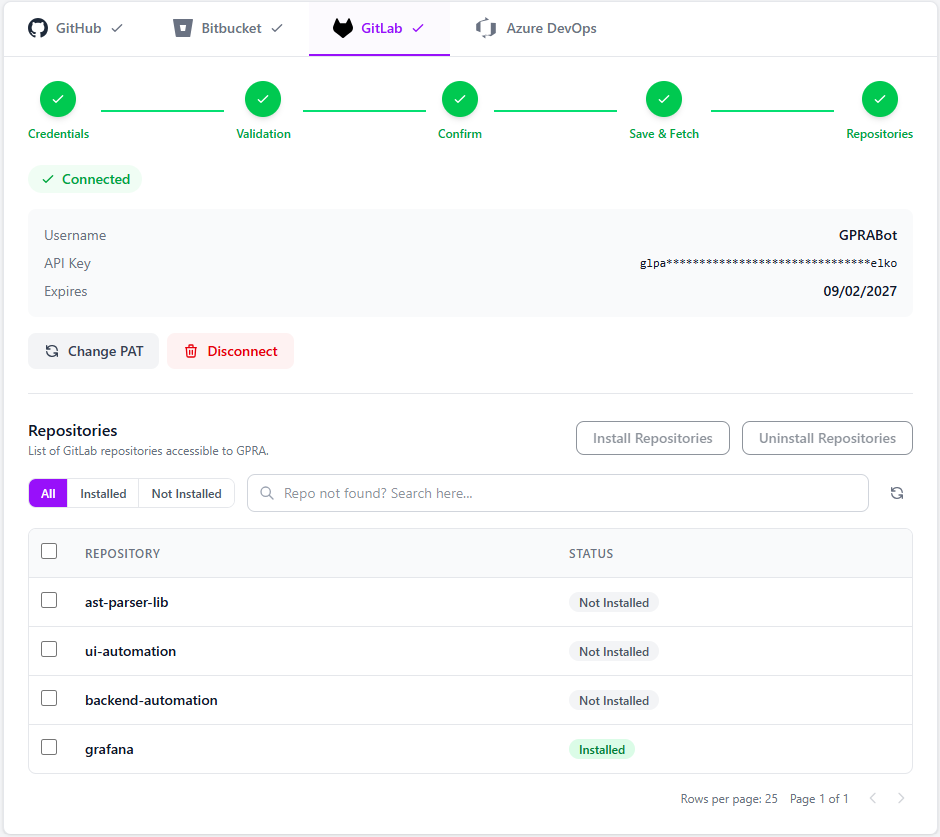
Automatic webhooks: Garth installs webhooks on selected repositories automatically. No manual webhook configuration is required. Webhooks are also removed automatically when you uninstall a repository.
Step 3: Activate and configure the repository
After installation, activate each repository under Agent Setup → PR Review → Repository Setup. Once a repository is activated, you can configure the following options:- Files to Exclude — specify file patterns that Garth should skip during reviews.
- Source Branches to Exclude — exclude MRs originating from certain branches.
- Destination Branches to Exclude — exclude MRs targeting certain branches.
- Auto Review — enable or disable automatic reviews for new MRs on this repository.
- Repository PR Review Guidelines — define custom review guidelines specific to this repository.
Troubleshooting
Webhook issues
Webhook issues
If Garth is not accessing repositories or reviewing merge requests:
- Check webhook status — go to the project’s settings in GitLab under Webhooks and verify the Garth webhook exists and is active.
- Manually delete the webhook if it exists but is not working.
- Refresh the repository page in the Garth app.
- Reinstall the webhook — untoggle and re-toggle the repository in the Garth dashboard.
Installation problems
Installation problems
If you cannot install Garth on a repository:
- Verify group/project membership — the service account must hold at least
Maintaineraccess to the target project to manage webhooks. - Check token scopes — confirm all required scopes (
api,read_api,read_user,read_repository,write_repository) are present on the token. - Re-validate the token — go to Settings → Integrations → GitLab in Garth and re-enter your credentials.
- Toggle the repository — uninstall and reinstall the repository from the Garth app to force a fresh webhook setup.
Not receiving reviews
Not receiving reviews
If Garth is installed but you are not receiving any reviews on your merge requests:
- Check repository activation — go to Agent Setup → PR Review → Repository Setup and confirm the repository is activated.
- Verify Auto Review is enabled — ensure the Auto Review toggle is turned on for the repository.
- Check branch exclusions — confirm the source or destination branch of your MR is not listed under Source Branches to Exclude or Destination Branches to Exclude.
- Check file exclusions — verify that the files changed in your MR are not covered by patterns in Files to Exclude.
Authentication errors
Authentication errors
If you receive authentication or permission errors:
- Check token expiry — GitLab Personal Access Tokens expire based on the date you set (or after 365 days by default). Regenerate and update the token in Garth if it has lapsed.
- Confirm the token type — use either a Group Access Token with
apiscope andMaintainerrole, or a Personal Access Token from the dedicated service account — not a personal user account. - Verify Group Owner status — the Garth user initiating the connection must hold GitLab Group Owner status.
- Re-authenticate — update the token in Settings → Integrations → GitLab within Garth and re-link with a freshly generated token.





